Understanding AWS CloudFront Edge Locations
I just wanted to bring up something totally cool that I hadnt quite realized before.
AWS Cloudfront follows the IATA airport code convention when naming their edge cache pop locations.
Have you ever been looking through your cloudfront logs and seen DFW55-C1 or ORD51-C1 in that 3rd column and wondered, what the heck do they actually mean?
Well yesterday I was investigating an incident that seemingly involved a single location. AWS CloudFront runs from many POPs (point-of-presence or also called edge location) around the world. A particular user’s requests would just time out, but not for other users. The problem seemed to be limited to this user’s geographic region. To figure out the problem, it was necessary to hop into the logs which is where I discovered which edge cache was getting hit. I then found there were more errors coming from the same one… Well, I’m not here to describe the troubleshooting, but to share the interesting bit of information I discovered. When looking up the edge cache’s code to find its location, I saw that it and others are using a newer naming convention.
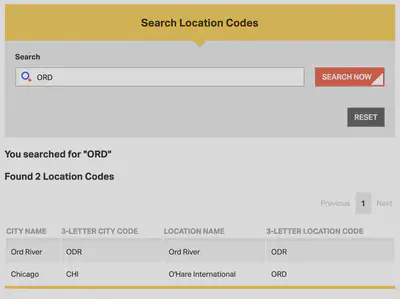
https://www.feitsui.com/en/article/3
You can always find this through a simple lookup as well. If you do a simple DNS lookup, for example:
$ nslookup example.com
Server: 8.8.8.8
Address: 8.8.8.8#53
Non-authoritative answer:
example.com canonical name = d111111abcdef8.cloudfront.net.
Name: d111111abcdef8.cloudfront.net
Address: 15.230.39.60
This gives us the IP address of the CloudFront Edge Cache. Next we perform a quick reverse dns lookup.
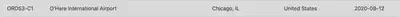
$ dig -x 15.230.39.60 +short
server-15.230.39.60.ORD53-C1.r.cloudfront.net.
That ORD53 is the important piece we need. Since AWS CloudFront follows a convention to name edge cache locations after IATA airport codes we can now search for the airport code at https://www.iata.org/en/publications/directories/code-search/. This reveals that the request was indeed coming from the edge cache in Chicago, Illinois due to the first 3-letter code of the name. ORD! Pretty cool huh?!